Blog
Are VPNs a Reliable Way to Avoid Government Surveillance?
Internet users worldwide are increasingly worried about their digital privacy. Logging every move, downloading, and online requests, internet service providers, and surveillance agencies could assemble very detailed user profiles and behavior. For front-end developers and web designers, it is vital to understand how to secure data transmissions when designing websites or applications. However, securing the application layer is only half of solving the problem of monitoring internet traffic.
Virtual Private Networks (VPNs) have been considered for a long time as a perfect layer of protection against surveillance and spying. They assure you that your data will be encrypted and protected from local tracking and mass data collection. As governments watch techniques continuously become more sophisticated, it is natural for users to ask if the protection provided by the VPN is enough to make their personal info invisible.
Classic surveillance operations by governments are no longer just about intercepting individual communication. They include bulk data collection, deep packet inspection, and extensive collaboration and sharing of information among global intelligence-sharing networks to analyze metadata on an unprecedented scale. Getting through this complicated situation requires knowing what your digital tools can secure, risks to your privacy, and what they can’t do to help you protect your personal data.
What is a VPN and How Does it Work (or Not Work)?

Before deciding whether these services are worth it, let us explain how they work. A VPN builds a secure and encrypted link between the user’s device and the remote server. Every time you visit a site or play free mobile games online, your internet activities are directed through this server.
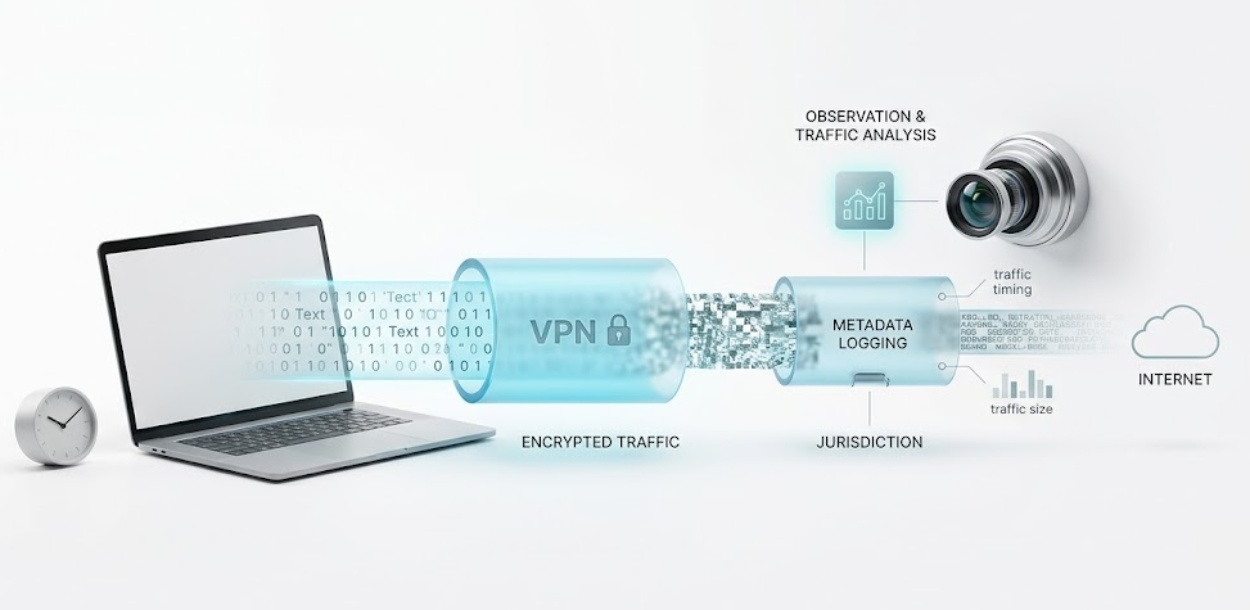
This not only hides your real IP address but also replaces it with that of the server so that it seems like your connection is coming from another place entirely. Encryption ensures that someone monitoring your internet connection, like your ISP or a government body, won’t be able to tell what websites you’re visiting – they’d only see a series of letters and numbers, effectively gibberish.
On the other hand, if a spy agency is capable of observing both the local network and the VPN server data center, it might use traffic correlation attacks. They match encrypted traffic to specific users by analyzing the timing and size of data packets when they enter and exit the server.
Adding to VPN Privacy Protection
Navigating the complex market of privacy tools requires reliable information and rigorous testing. According to data from VPNOverview.com, not all services provide the same level of security or transparency. VPNOverview evaluates these services by thoroughly testing their encryption protocols, analyzing their server networks, and scrutinizing their logging policies. This ensures users have access to objective insights when selecting a tool to secure their network traffic. Building a robust defense strategy requires relying on verified VPN privacy protection methods, and platforms like VPNOverview play a crucial role in highlighting which providers actually deliver on their promises.
More Than IP Addresses: Government Surveillance Methods
Governments have developed highly effective mechanisms to trace individuals across the web. Sure, changing your IP address is one of the measures in the right direction. However, it is typically very far from enough to stop someone who is determined to track you completely. Deep Packet Inspection (DPI) is a powerful tool capable of analyzing Internet traffic to a very fine level – even identifying what kind of traffic it is (for instance, that a VPN is being used). Many repressive states employ these methods as a part of their VPN blocking campaigns.
And there’s more. Tracking via endpoints – i.e., web trackers, browser fingerprinting, and cookie-based tracking – works no matter where you are physically and even if your IP address changes. If your front-end web design incorporates invasive third-party tracking scripts, VPN won’t be able to stop those scripts from identifying users.
Moreover, global intelligence alliances, such as the Five Eyes, share surveillance data across borders. If your chosen service provider operates within these jurisdictions and keeps records of your activity, a government subpoena could force them to hand over that data.
VPN Advantages to Surveillance
With the right level of VPN privacy protection, most people will be able to fend off the kind of mass surveillance that is carried out in an indiscriminate and untargeted fashion. These services, encrypting your internet connection, will also stop your regular ISP from keeping your logs of websites visited and handing these logs to the authorities.
Another use case that VPNs serve very well is the unblocking of geo-restricted content and going around local censorship. Oppressed citizens in closed societies quite often depend on their encrypted VPN tunnels for all their internet-related needs, such as fresh and free communication and reading independent, uncensored news.
| Surveillance Method | VPN Countermeasure | Effectiveness |
| ISP Data Logging | Encrypts all DNS requests and network traffic | High |
| IP Address Tracking | Routes traffic through a remote server | High |
| Deep Packet Inspection | Uses obfuscated servers to hide protocol metadata | Medium |
| Browser Fingerprinting | None (operates at the network level) | Low |
What are the Weaknesses of VPNs?
The most serious vulnerability of any privacy tool is the human element behind it. If the provider keeps detailed connection logs, it is entirely possible for the VPN privacy protection to be compromised. Some companies, even those who declare “no-log” in their marketing materials, have been caught on several occasions by the press handing user logs over to law enforcement.
Strong government-grade firewalls will almost certainly become yet another huge obstacle encountered here. Some are so high-tech that they can identify and actively block the IP addresses that are known to belong to popular privacy providers. There are also obfuscation techniques that attempt to make encrypted traffic look like regular HTTPS data, but the truth is, there is always a struggle to stay ahead of state firewalls at any point in time.
End-user vulnerabilities can completely bypass the network security as well. You could have the most secure web design and use very safe browsing habits, but if you download malware or get tricked into giving your details by phishing, your device will be compromised from the inside. Nothing at the network level will be able to save you if you have an already infected device.
How to Pick a VPN for Privacy
Getting one that really provides you with robust VPN privacy protection means that you need to ignore the marketing claims and go beyond them. Please check the service company’s policies and infrastructure to ensure your data will be secure.
When selecting your solution provider, think about these things:
- No-log policies that are really strict: You want to make sure the company isn’t tracking your IP address, browsing history, or connection timestamps.
- Security audits by independent parties: Go for services that trust third-party security firms to come in and verify their no-log claims, as well as test their infrastructure.
- Encryption protocols that are robust: They should use modern standards such as WireGuard or OpenVPN together with AES-256 encryption.
- A good legal jurisdiction: This means the company should be located in a country that does not have mandatory data retention laws or is part of global intelligence alliances.
- Servers running on RAM only: Every restart wipes these instantly, which means it’s impossible to keep logs long-term.
If you need a starting point, you can consult trusted sources and reviews from VPNOverview to identify providers that meet the stringent benchmarks.
Besides VPNs: A Multi-faceted Strategy to Digital Privacy
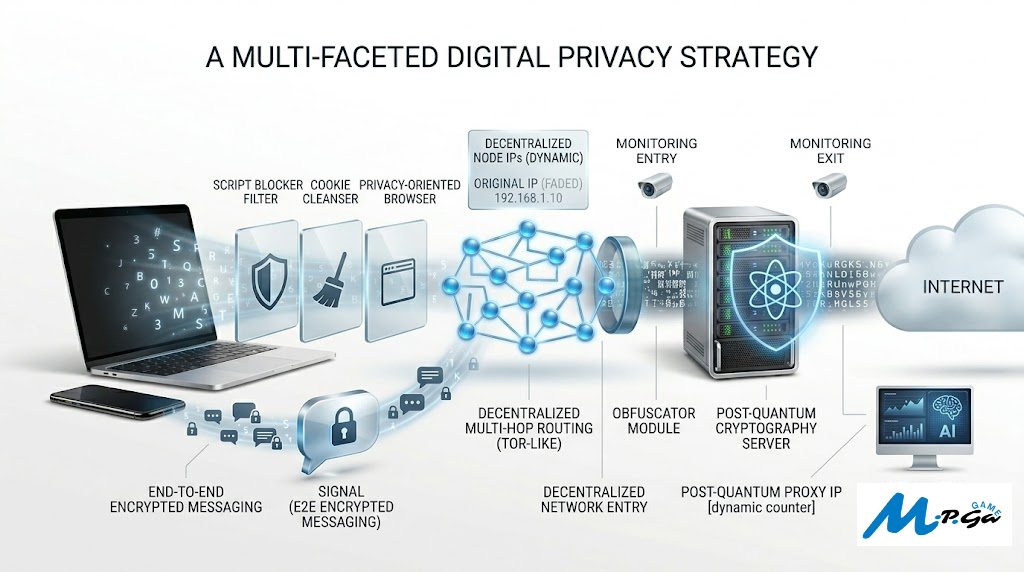
Counting on one single tool is a major flaw in any security plan, for that matter. Real digital privacy calls for a multi-layered approach. These days, for total anonymity, activists and journalists are often using Tor Browser. The traffic is routed through multiple decentralized nodes in this browser, which significantly makes it difficult to correlate traffic and attack users based on it.
When it comes to secure communication, there is no substitute for using end-to-end encrypted messaging apps like Signal. Besides that, good digital hygiene is essential. Start using privacy-oriented browsers, installing script blockers, and regularly clearing your cookies. For web developers, integrating privacy-by-design into web applications is a great way to ensure users’ protection even before they face the need to hide their connections.
The outlook for VPNs and the privacy realm is changing dramatically. Advances in quantum computing are rapidly approaching the point where the mathematical foundations of encryption algorithms used today may be broken. Cybersecurity experts are working on developing post-quantum cryptography methods so that VPN privacy can still be guaranteed in the future.
On the other hand, privacy-enhancing technologies are changing by incorporating features like decentralized networks and multi-hop routing. Managers of government surveillance systems are using machine learning to detect traffic patterns, so if people want to stay hidden users will have to get much more sophisticated at the use of obfuscators.
Protecting Your Digital Rights: A Continuous Struggle
Keeping your personal information from being accessed by government surveillance is something that you cannot achieve once and then forget about. Even though a top-notch encrypted connection can almost always prevent local monitoring and bulk data collection, it still cannot be considered a panacea for tracking at the level of the browser or fingerprinting.
Learning about the restrictions of your network tools, selecting top-tier providers verified by platforms such as VPNOverview, and adopting a broad approach to digital security are steps toward taking control of your online identity.
Make a habit out of auditing the privacy tools that you use, browser settings, and the overall environment that surrounds your data to make sure that it remains under your complete control.
Final Conclusion
VPNs remain one of the most effective and accessible tools for improving online privacy, but they are not a complete solution to government surveillance. A high-quality VPN can successfully encrypt your internet traffic, hide your IP address, and reduce exposure to ISP monitoring and bulk data collection. For most everyday users, this level of protection significantly improves digital privacy and security.
However, modern surveillance systems operate far beyond simple IP tracking. Governments and intelligence agencies increasingly rely on deep packet inspection, browser fingerprinting, metadata analysis, tracking cookies, endpoint compromises, and global intelligence-sharing agreements. In situations involving targeted investigations or advanced state-level monitoring, a VPN alone may not be enough to guarantee anonymity.
The effectiveness of VPN privacy protection depends heavily on the provider itself. Services with strict no-log policies, independent security audits, modern encryption protocols, and privacy-friendly legal jurisdictions offer far better protection than free or poorly regulated alternatives. Users should carefully research providers rather than relying solely on marketing claims.
True digital privacy requires a layered strategy. Combining a VPN with privacy-focused browsers, secure messaging applications, tracker blockers, strong passwords, multi-factor authentication, and safe browsing habits provides far stronger protection than any single tool alone. For journalists, activists, researchers, or users operating under restrictive governments, advanced privacy solutions such as the Tor network and encrypted communication platforms may also be necessary.
Finally, VPNs are reliable for reducing mass surveillance and improving online privacy. Still, they should be viewed as one component of a broader cybersecurity and privacy strategy rather than a magical invisibility cloak.
Disclaimer
This article is intended for educational and informational purposes only. It does not constitute legal, cybersecurity, or professional privacy advice. The effectiveness of VPNs and other privacy tools may vary depending on local laws, internet regulations, provider policies, user behavior, and evolving surveillance technologies. Users are responsible for complying with the laws and regulations applicable in their country or region when using VPN services or privacy-enhancing technologies.
