Blog
How to Protect Your Privacy When Using Crypto Exchanges: Tips from the Swapter team

Cryptocurrency is often celebrated as the pinnacle of financial freedom and privacy. Yet, the irony is that when we log into centralized exchanges, even through seemingly secure devices, we leave behind digital footprints that could reveal more about us than we realize. Whether you use established platforms or newer services like Swapter, every connection leaves traces that can compromise your privacy.
While most discussions about crypto privacy focus on wallet addresses and transaction obfuscation, one critical risk is often overlooked: your IP address. This unique identifier can link your real-world identity to your cryptocurrency activities long after the fact. Protecting it is no longer optional-it’s essential.
IP Address Reality Check: Your Digital Fingerprint Problem
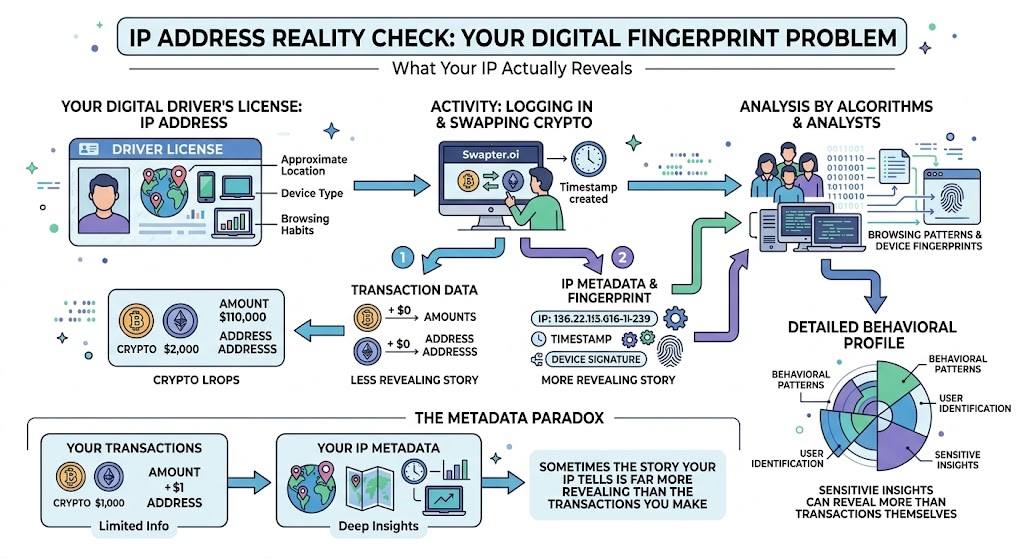
What Your IP Actually Reveals
Think of your IP address as a digital driver’s license. It may not display your photo, but it can reveal your approximate location, device type, and browsing habits. Every time you log in to swap cryptocurrencies with Swapter.oi, you leave a timestamped record of your activity. Analysts and algorithms can cross-reference this with browsing patterns and device fingerprints to build detailed behavioral profiles-sometimes even revealing more than your transactions themselves. This phenomenon is known as the “metadata paradox”: sometimes the story your IP tells is far more revealing than the transactions you make.
How Exchanges Use Your IP: Security and Surveillance
| Aspect | Purpose / Description | Implications for Users | Best Practice / Mitigation |
|---|---|---|---|
| Surveillance Infrastructure | Exchanges collect IPs to detect suspicious logins, prevent fraud, and comply with KYC/AML regulations | Your IP becomes linked to your trading activity; even aggregated data may be analyzed or shared | Use privacy tools like VPNs or Tor to reduce direct IP exposure; separate devices/accounts where possible |
| Data Retention | IP logs are stored for months or indefinitely depending on local laws | Historical IP records can correlate pseudonymous activity with real identity | Minimize identifiable metadata when trading; maintain operational security practices (OPSEC) |
Privacy Tech Stack: Concealing Your IP
| Tool | Key Benefit | How It Works | Advantages | Limitations | Best Use Case |
|---|---|---|---|---|---|
| VPN (Virtual Private Network) | Strong everyday privacy | Encrypts internet traffic and masks your IP address | Secure, widely accessible, good balance of speed and privacy | Requires trust in provider’s “no logs” policy | Daily crypto trading with enhanced privacy |
| Tor (The Onion Router) | Maximum anonymity | Routes traffic through multiple volunteer-operated nodes | High level of anonymity, difficult to trace activity | Slow speeds, not ideal for time-sensitive trading | Privacy-focused users prioritizing anonymity over speed |
| Proxy Servers | Basic IP masking | Redirects traffic through another server | Fast, simple, easy to set up | Lacks encryption, weaker privacy, potential data risks | Temporary or supplementary privacy solution |
Strategic Privacy: Defense in Depth
| Strategy | Key Focus | Description | Advantages | Considerations / Risks | Best Practice |
|---|---|---|---|---|---|
| Layered Approach | Multi-tool protection | Combine VPNs, privacy-focused browsers, tracker blockers, and separate devices to create overlapping privacy layers | Reduces risk if one layer is compromised; stronger overall security | Complexity can be high; requires setup and ongoing management | Use multiple complementary tools for all crypto activity |
| Operational Security (OPSEC) | Human behavior | Carefully manage online behavior, device usage, and timing of trades to avoid identity correlation | Prevents human errors from undermining technological measures | Mistakes in posting or linking accounts can expose identity | Avoid sharing crypto activity publicly; separate anonymous and identified accounts |
Privacy Trade-offs: Performance, Complexity, and Legal Risks
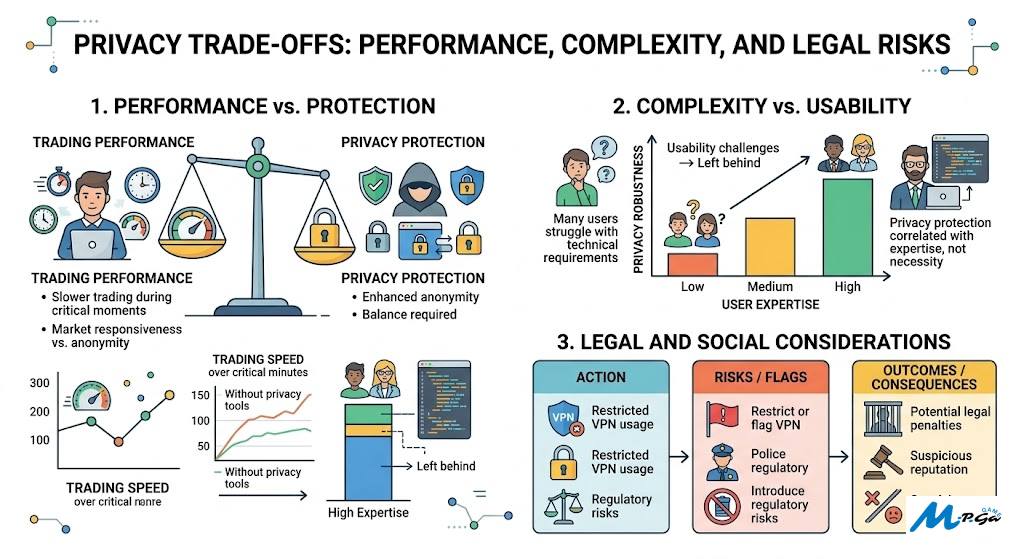
- Performance vs. Protection: Privacy tools may slow trading during critical moments, creating a balance between anonymity and market responsiveness.
- Complexity vs. Usability: Implementing robust privacy requires technical knowledge. Many users struggle, leaving privacy protection correlated with expertise rather than necessity.
- Legal and Social Considerations: Some regions restrict VPN usage or flag it as suspicious. Privacy tools may reduce surveillance but introduce regulatory risks.
Conclusion
Protecting your IP address is an essential step toward true crypto privacy. Platforms like Swapter provide convenient, secure alternatives for exchanging cryptocurrency, but even there, your digital footprint can reveal more than your transactions. By combining technological solutions like VPNs or Tor with operational security practices and a layered privacy strategy, you can reclaim control over your online identity.
Disclaimer
This article is intended for informational purposes only and does not constitute financial, legal, or cybersecurity advice. While privacy tools such as VPNs, Tor, and proxy servers can enhance anonymity, their effectiveness depends on proper usage and individual circumstances. Users are responsible for complying with local laws and regulations when using cryptocurrency platforms and privacy technologies. Always conduct your own research or consult qualified professionals before making decisions related to digital privacy or cryptocurrency trading.
References
- Böhme, R., Christin, N., Edelman, B., & Moore, T. (2015). Bitcoin: Economics, technology, and governance. Journal of Economic Perspectives, 29(2), 213–238. https://doi.org/10.1257/jep.29.2.213
- Kahn, C. M., Rivadeneyra, F., & Wong, T.-N. (2018). Should the central bank issue e-money? Bank of Canada Staff Working Paper. https://doi.org/10.2139/ssrn.3244366
- Meiklejohn, S., Pomarole, M., Jordan, G., Levchenko, K., McCoy, D., Voelker, G. M., & Savage, S. (2013). A fistful of bitcoins: Characterizing payments among men with no names. Proceedings of the ACM Internet Measurement Conference, 127–140. https://doi.org/10.1145/2504730.2504747
- Reid, F., & Harrigan, M. (2013). An analysis of anonymity in the Bitcoin system. Security and Privacy in Social Networks, 197–223. https://doi.org/10.1007/978-1-4614-4139-7_10
- Dingledine, R., Mathewson, N., & Syverson, P. (2004). Tor: The second-generation onion router. Proceedings of the 13th USENIX Security Symposium, 303–320. https://doi.org/10.5555/1251375.1251396
- Chaabane, A., Manils, P., & Kaafar, M. A. (2010). Digging into anonymous traffic: A deep analysis of the Tor anonymizing network. 2010 Fourth International Conference on Network and System Security, 167–174. https://doi.org/10.1109/NSS.2010.18
- AlSabah, M., Bauer, K., Nunnery, C., & Goldberg, I. (2013). Performance and security improvements for Tor. ACM Transactions on Information and System Security, 16(2), 1–27. https://doi.org/10.1145/2487222.2487223
- Dwivedi, Y. K., Hughes, L., Ismagilova, E., et al. (2021). Artificial intelligence (AI): Multidisciplinary perspectives on emerging challenges, opportunities, and agenda for research. International Journal of Information Management, 57, 101994. https://doi.org/10.1016/j.ijinfomgt.2019.08.002
